These vulnerabilities present in various scenarios allow adversaries to exploit flaws in Bluetooth connections. The BLUFFS attacks primarily focus on the generation of compromised session keys during the pairing process of Bluetooth devices, which are intended to establish secure connections. Such compromised keys pose a risk of unauthorized access to data transmitted via Bluetooth.
A key risk identified involves a Man-in-the-Middle (MITM) attack scenario. In this, the attacker impersonates paired or bonded devices, forcing them to use legacy encryption methods and, if not already set, to adopt the Peripheral role. This approach enables the attacker to impose the use of the lowest supported encryption key length and to manipulate nonce values in the encryption key generation process. Successful execution of this attack can lead to repeated use of the same encryption key in multiple sessions within close proximity.
Furthermore, if a reduced encryption key length is agreed upon, a MITM attacker could employ brute force methods to decode the encryption key. By enforcing the use of the same encryption key, the attacker can render both past and future sessions susceptible to decryption. While the recommended minimum encryption key length for BR/EDR encrypted sessions is 7 octets, considered robust against real-time brute force attacks, an attacker in close physical proximity to the targeted devices might accumulate sufficient data to compromise a single session key.
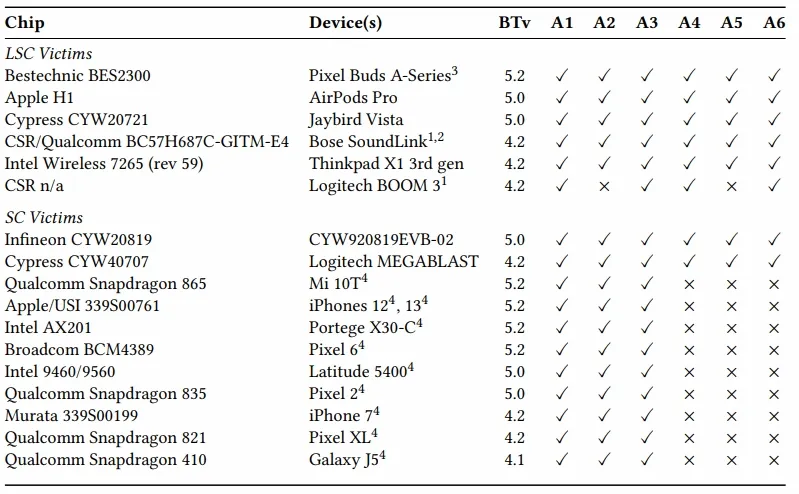
To mitigate these vulnerabilities, it is advised to refuse service-level connections on an encrypted baseband link with key strengths below 7 octets. For systems capable of consistently using Security Mode 4 Level 4, rejecting connections with a key strength below 16 octets is recommended. Additionally, the activation of Secure Connections Only Mode on both involved devices can significantly enhance key strength. Tests on various devices indicate that a wide range of devices are vulnerable to at least three different forms of these attacks. Notably, these attacks are only feasible when two susceptible Bluetooth devices are within wireless range of each other. Since these vulnerabilities are inherent in the Bluetooth standard's core architecture, they could potentially affect a vast number of devices released since 2014.
The Bluetooth Special Interest Group has been informed about these vulnerabilities and advises manufacturers to refuse keys shorter than seven octets and to consistently implement Secure Connections Only Mode as effective countermeasures.
Sources: Bluetooth , Eurecom , Bleeping Computer