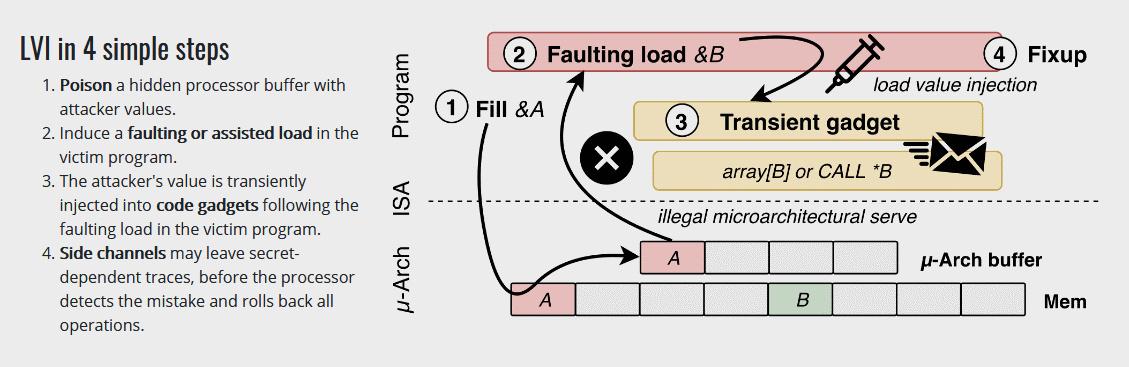
Not to confuse the vulnerability I mentioned a few days ago. Computer security researchers involved in the discovery of the Meltdown and Spectre vulnerabilities affecting many modern processors have developed a related attack technique called Load Value Injection (LVI).
This time the problem is called 'LVI-LFB', which stands for Load Value Injection in the Line Fill Buffers. It has the CVE-2020-0551 attribute and, like many of the previously discovered issues, uses speculative execution.
The problem likely occurs towards Intel chips from Ivy Bridge generation up to and including Comet Lake, the researchers do not exclude that chips from other brands are not susceptible either as all processors that are susceptible to Meltdown could potentially be at risk. In addition, updates in the microcode, which Intel is likely to have in the works, could cause calculations to be performed 2 to 19 times slower on certain workloads, so this is a big one. The expectation is that these software updates simply will not get installed by many due to that performance hit.
The attack relies on microarchitectural data leakage to inject and execute malicious code in a way that breaks the confidentiality of modern Intel systems. Intel's processors, already weighed down by defenses deployed against side-channel attacks over the past two years, could get slower still if they try to thwart this latest vulnerability: prototype compiler changes, for full mitigation, have produced performance reductions ranging from 2x to 19x. That's because LVI protection involves compiler and assembler updates that insert extra x86 instructions (lfence) and replace problematic instructions (such as ret) with functionally equivalent but more verbose instruction sequences. In a paper scheduled to be published today, March 10, in a coordinated disclosure announcement with Intel, boffins from KU Leuven, Worcester Polytechnic Institute, Graz University of Technology, University of Michigan, and University of Adelaide, describe LVI as a reverse-Meltdown attack. Instead of leaking data from memory, it injects transient load values during a faulting or assisted load operation to perform some malicious action.
The threat scenario involves a local adversary trying to obtain secrets (like passwords or encryption keys) from an operating system kernel, an OS process, or an SGX enclave. For SGX, root OS privileges are assumed – SGX was designed to protect against root-level attacks. With such secrets, more extensive compromise becomes possible.
It turns out that Meltdown, a technique for pulling data from a computer's memory, can be turned around to put data back in, thereby poisoning data stored in memory during brief, speculative operations. Though the data gets thrown away after these short-lived tasks, it can still cause trouble.
Source: The Register
New Meltdown like Vulnerability hits Intel: LVI Security vulnerabilities