Over the weekend a new report surfaced online, indicating that AMD would have Side Channel Vulnerabilities in their processors. The paper released by the Graz University of Technology detailed two new "Take A Way" attacks, Collide+Probe and Load+Reload, that can leak secret data from AMD processors by manipulating the L1D cache predictor.
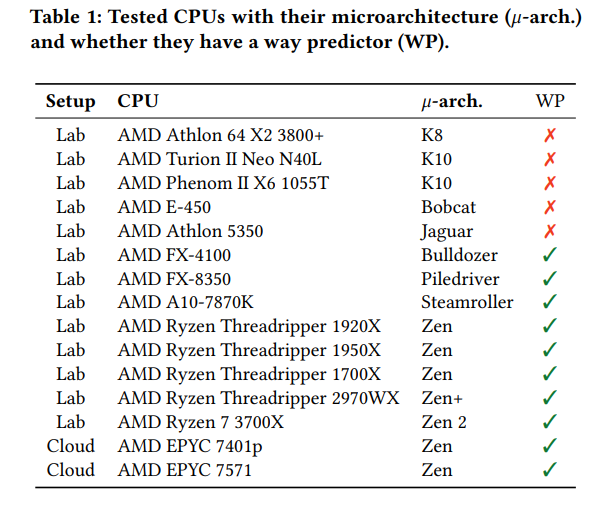
The researchers claim that the vulnerability impacts all AMD processors from 2011 to 2019. The research team said it notified AMD about the two problems in August 2019, however, the company has not publicly addressed the two problems, nor has it released microcode updates (CPU firmware).
“We reverse-engineered AMD’s L1D cache way predictor in microarchitectures from 2011 to 2019, resulting in two new attack techniques,” the researchers said.
Both exploit the "way predictor" for the Level 1 cache (meant to boost the efficiency of cache access) to leak memory content. The Collide+Probe attack lets an intruder monitor memory access without having to know physical addresses or shared memory, while Load+Reload is a more secretive method that uses shared memory without invalidating the cache line. The team took advantage of the flaws using JavaScript in common browsers like Chrome and Firefox. While Take A Way only exposes out a small amount of information compared to Meltdown or Spectre, that was enough for the investigators to access AES encryption keys. It would be possible to address the flaw through a mix of hardware and software, the researchers said, although it's not certain how much this would affect performance.
AMD posted the following statement on its website
AMD responded to the publication of these security vulnerabilities via a security advisory on its website, acknowledging the security exploits and stating they were not a new form of side-channel attack.
“We are aware of a new white paper that claims potential security exploits in AMD CPUs, whereby a malicious actor could manipulate a cache-related feature to potentially transmit user data in an unintended way,” AMD said.
“The researchers then pair this data path with known and mitigated software or speculative execution side-channel vulnerabilities. AMD believes these are not new speculation-based attacks.”
AMD said it recommended users follow the steps be taken by users to help mitigate against side-channel attacks:
- Keep your operating system up-to-date by operating at the latest version revisions of platform software and firmware, which include existing mitigations for speculation-based vulnerabilities
- Following secure coding methodologies
- Implementing the latest patched versions of critical libraries, including those susceptible to side-channel attacks
- Utilizing safe computer practices and running antivirus software
The advisory does not point to any mitigations for the attack in question, merely citing other mitigated speculative executions that were used as a vehicle to attack the L1D cache predictor.
The Graz University of Technology performed a lot of Vulnerability tests ion the past, but the reality is also that they are partially funded by intel, it seems. The paper mentions this, and really, just read it: "Additional funding was provided by generous gifts from Intel. Any opinions, findings, and conclusions or recommendations expressed in this paper are those of the authors and do not necessarily reflect the views of the funding parties." Albeit a curiosity, the co-authors of the Intel-funded study also revealed Intel's vulnerabilities in the past.