Positive Technologies, which in September said it has a way to drill into Intel's secretive Management Engine technology hideen in its chipsets, dropped more details. The IME is a separate controller on the Intel Platform Platform Controller Hub (PCH), which has access to communication between the processor and other hardware.
The biz has already promised to demonstrate a so-called God-mode hack this December, saying they've found a way for "an attacker of the machine to run unsigned code in the Platform Controller Hub on any motherboard." Reports the register:
For those who don't know, for various processor chipset lines, Intel's Management Engine sits inside the Platform Controller Hub, and acts as a computer within your computer. It runs its own OS, on its own CPU, and allows sysadmins to remotely control, configure and wipe machines over a network. This is useful when you're managing large numbers of computers, especially when an endpoint's main operating system breaks down and the thing won't even boot properly. Getting into and hijacking the Management Engine means you can take full control of a box, underneath and out of sight of whatever OS, hypervisor or antivirus is installed. This powerful God-mode technology is barely documented and supposedly locked down to prevent miscreants from hijacking and exploiting the engine to silently spy on users or steal corporate data. Positive says it's found a way to commandeer the Management Engine, which is bad news for organizations with the technology deployed.
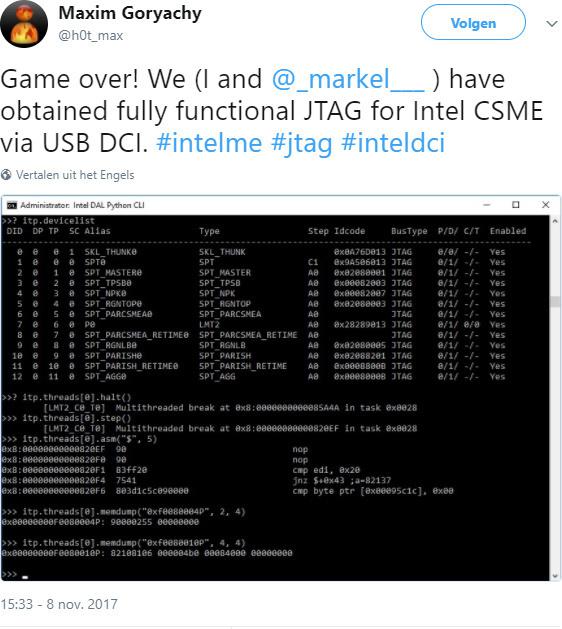
For some details, we'll have to wait, but what's known now is bad enough: Positive has confirmed that recent revisions of Intel's Management Engine (IME) feature Joint Test Action Group (JTAG) debugging ports that can be reached over USB. JTAG grants you pretty low-level access to code running on a chip, and thus we can now delve into the firmware driving the Management Engine.
With knowledge of the firmware internals, security vulnerabilities can be found and potentially remotely exploited at a later date. Alternatively, an attacker can slip into the USB port and meddle the engine as required right there and then. There have been long-running fears IME is insecure, which is not great as it's built right into the chipset: it's a black box of exploitable bugs, as was confirmed in May when researchers noticed you could administer the Active Management Technology software suite running on the microcontroller with an empty credential string over a network.
Intel CPUs since Skylake susceptible to USB vulnerability